Search results for "malware"
-

 515Malware
515MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware
Threat actors have been observed making use of fake websites masquerading as legitimate antivirus solutions from Avast, Bitdefender, and Malwarebytes to propagate...
-

 767Malware
767MalwareJAVS Courtroom Recording Software Backdoored – Deploys RustDoor Malware
Malicious actors have backdoored the installer associated with courtroom video recording software developed by Justice AV Solutions (JAVS) to deliver malware that’s...
-
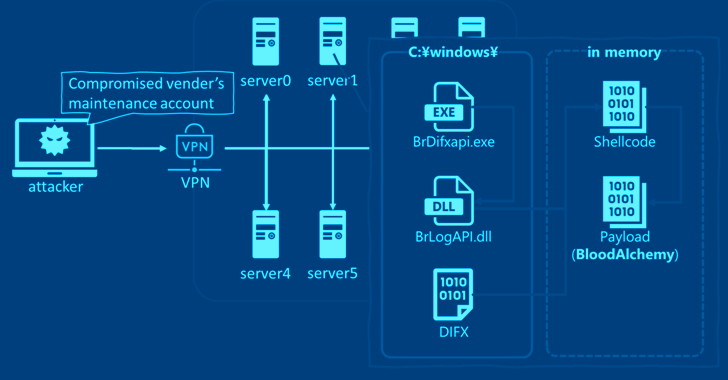
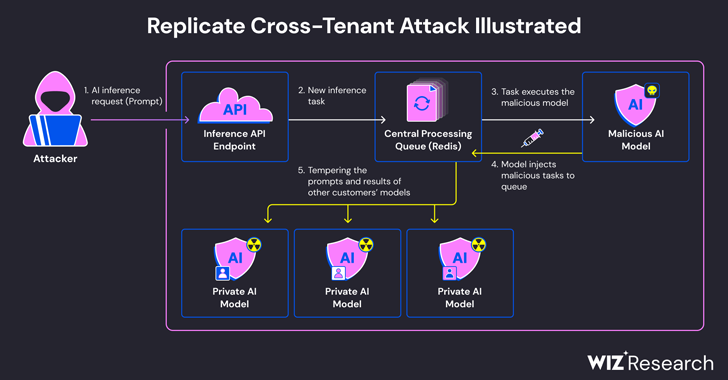
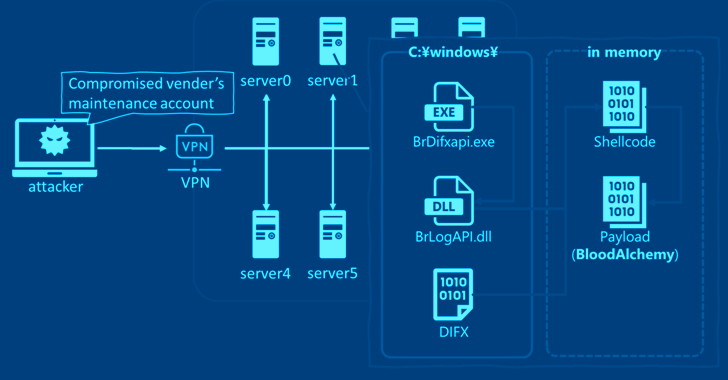 2.3KMalware
2.3KMalwareStealthy BLOODALCHEMY Malware Targeting ASEAN Government Networks
Cybersecurity researchers have discovered that the malware known as BLOODALCHEMY used in attacks targeting government organizations in Southern and Southeastern Asia is...
-
 1.8KMalware
1.8KMalwareMalware Delivery via Cloud Services Exploits Unicode Trick to Deceive Users
A new attack campaign dubbed CLOUD#REVERSER has been observed leveraging legitimate cloud storage services like Google Drive and Dropbox to stage malicious...
-
 3.0KData Breach
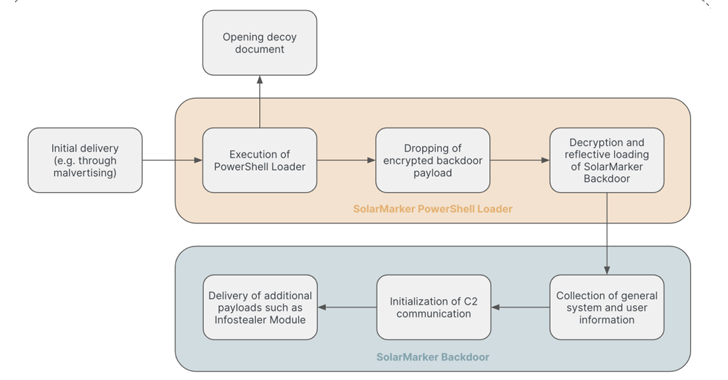
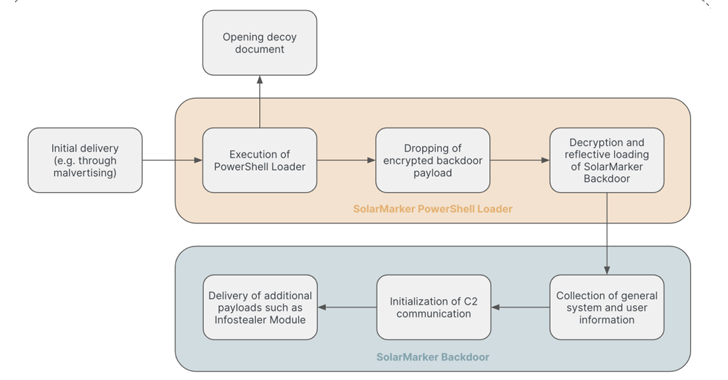
3.0KData BreachSolarMarker Malware Evolves to Resist Takedown Attempts with Multi-Tiered Infrastructure
The persistent threat actors behind the SolarMarker information-stealing malware have established a multi-tiered infrastructure to complicate law enforcement takedown efforts, new findings...
-

 4.3KVulnerabilities
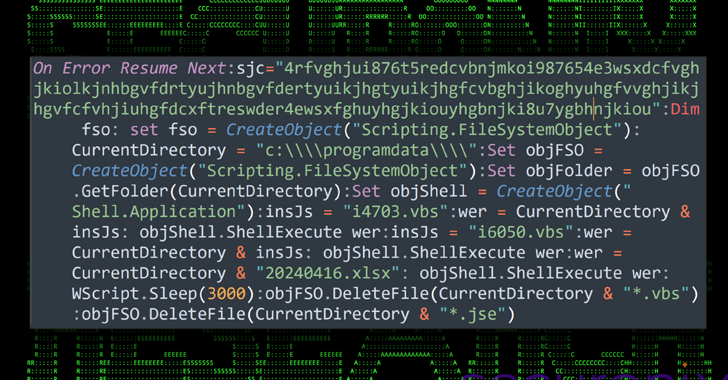
4.3KVulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
Multiple threat actors are weaponizing a design flaw in Foxit PDF Reader to deliver a variety of malware such as Agent Tesla,...
-

 3.7KMalware
3.7KMalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
A “multi-faceted campaign” has been observed abusing legitimate services like GitHub and FileZilla to deliver an array of stealer malware and banking...
-

 1.6KMalware
1.6KMalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
Cybersecurity researchers have observed a spike in email phishing campaigns starting early March 2024 that delivers Latrodectus, a nascent malware loader believed...
-
 4.3KMalware
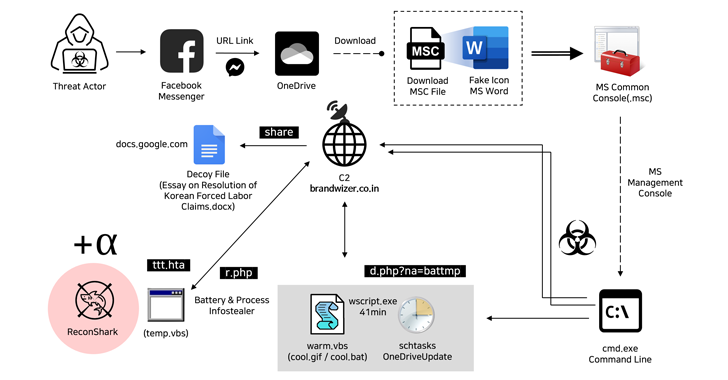
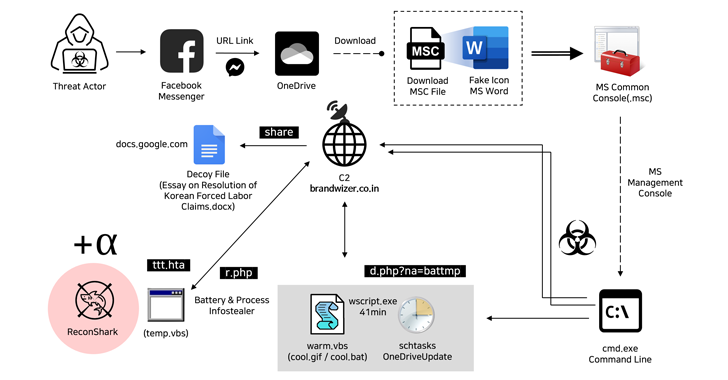
4.3KMalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
The North Korea-linked Kimsuky hacking group has been attributed to a new social engineering attack that employs fictitious Facebook accounts to targets...
-

 4.8KMalware
4.8KMalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
A malware botnet called Ebury is estimated to have compromised 400,000 Linux servers since 2009, out of which more than 100,000 were...
-

 3.6KMalware
3.6KMalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
The North Korean threat actor tracked as Kimsuky has been observed deploying a previously undocumented Golang-based malware dubbed Durian as part of...
-

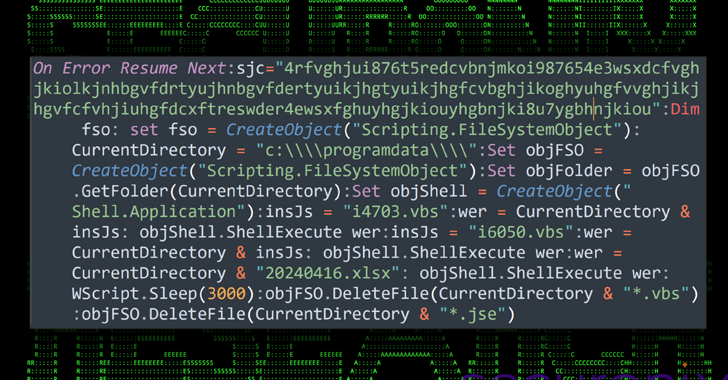
 3.6KCyber Attack
3.6KCyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
Polish government institutions have been targeted as part of a large-scale malware campaign orchestrated by a Russia-linked nation-state actor called APT28. “The...
-

 1.8KMalware
1.8KMalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
A newer version of a malware loader called Hijack Loader has been observed incorporating an updated set of anti-analysis techniques to fly...
-

 3.5KMalware
3.5KMalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
Threat actors have been increasingly weaponizing Microsoft Graph API for malicious purposes with the aim of evading detection. This is done to...
-

 2.4KData Breach
2.4KData BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
A new malware called Cuttlefish is targeting small office and home office (SOHO) routers with the goal of stealthily monitoring all traffic...
-

 4.9KCyber Attack
4.9KCyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
Cybersecurity researchers have discovered a previously undocumented malware targeting Android devices that uses compromised WordPress sites as relays for its actual command-and-control...
-

 2.5KMalware
2.5KMalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
The authors behind the resurfaced ZLoader malware have added a feature that was originally present in the Zeus banking trojan that it’s...
-

 3.4KMalware
3.4KMalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
The cybersecurity community has recently been abuzz with discussions surrounding CVE-2024-3400, a critical vulnerability affecting Palo Alto Networks’ PAN-OS, used in their...
-

 3.5KMalware
3.5KMalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick...
-

 686Malware
686MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. “Brokewell is a typical modern banking malware...
-

 3.7KMalware
3.7KMalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery...